Drift Protocol Exploit Drains Up to $285 Million Across Multi-Chain Transfers

Attack traced to nonce-based transaction abuse as Solana officials call incident isolated
TL;DR
- Drift Protocol lost $200M-$285M in a multi-asset exploit executed in under a minute after weeks of preparation
- Attack involved durable nonce-based pre-signed transactions enabling unauthorized admin actions
- Funds were converted, bridged, and consolidated into over 130,000 ETH while criticism targeted Circle’s response
We’ve launched the all-new COIN360 Perp DEX, built for traders who move fast!
Trade 130+ assets with up to 100× leverage, enjoy instant order placement and low-slippage swaps, and earn USDC passive yield while climbing the leaderboard. Your trades deserve more than speed — they deserve mastery.
Drift Protocol suffered a major exploit between April 1 and April 2, 2026, draining between $200 million and $285 million in assets, with the platform halting deposits and withdrawals while investigating what it described as an active attack driven by unauthorized administrative access rather than a smart contract flaw.
Drift halts operations as exploit unfolds
Drift Protocol said it was “experiencing an active attack” and immediately suspended deposits and withdrawals, warning users, “This is not an April Fools joke.” The platform said it was working with multiple security firms, bridges, and exchanges as the situation developed in real time.
Initial estimates placed losses at more than $200 million, with later tracking raising figures to more than $270 million, about $280 million, and up to $285 million as blockchain analysis firms followed the movement of funds across chains.
Vault balances collapse within minutes
Onchain data showed the protocol’s vault balance dropping sharply from $309 million to $41 million within minutes, with the exploit affecting more than 15 different token types, indicating a broad compromise of platform-controlled assets rather than a single pool or asset class.
Durable nonce mechanism enabled delayed execution
Drift later said the exploit involved durable nonce-based, pre-signed transactions that allowed an attacker to execute previously authorized actions at a later time under unintended conditions. On Solana, durable nonces allow transactions to bypass the typical 60-90 second expiration window, enabling delayed execution for operational flexibility.
The team’s explanation described how the exploiter used this mechanism to pre-sign administrative transactions weeks in advance, then executed them in rapid succession, bypassing expected safeguards. The execution phase reportedly took less than one minute, despite requiring more than a week of preparation.
Drift said the attacker used these transactions to gain unauthorized administrative access, enabling large-scale asset transfers across the protocol.
Dispute over root cause: keys vs operational security
The incident has not been fully resolved, and explanations vary across sources.
Some findings stated “there was no bug” and no private key was cracked, while blockchain security firm PeckShield’s founder Jiang Xuxian said, “the admin keys behind Drift were definitely leaked or compromised.”
Omer Goldberg, founder of Chaos Labs, emphasized operational risk rather than code failure, with guidance that teams should audit admin keys, not just code, reflecting concerns around privileged access rather than smart contract vulnerabilities.
Funds rapidly converted and bridged across chains
After draining assets, the attacker reportedly converted holdings into stablecoins and bridged them out of the Solana ecosystem.
Drift and related reporting said funds were largely swapped into USDC, then bridged from Solana to Ethereum using CCTP, before being consolidated into ether.
At one stage, the attacker was reported to have accumulated 130,262 ETH worth about $267 million, indicating a structured post-exploit conversion strategy.
Circle response draws criticism over frozen funds
The exploit triggered criticism toward Circle after the attacker moved funds into USDC.
ZachXBT said, “6 hours is how long Circle had to freeze stolen funds from the $280M+ Drift hack,” adding that Circle failed to act despite observing more than 100 transactions hours after the incident began.
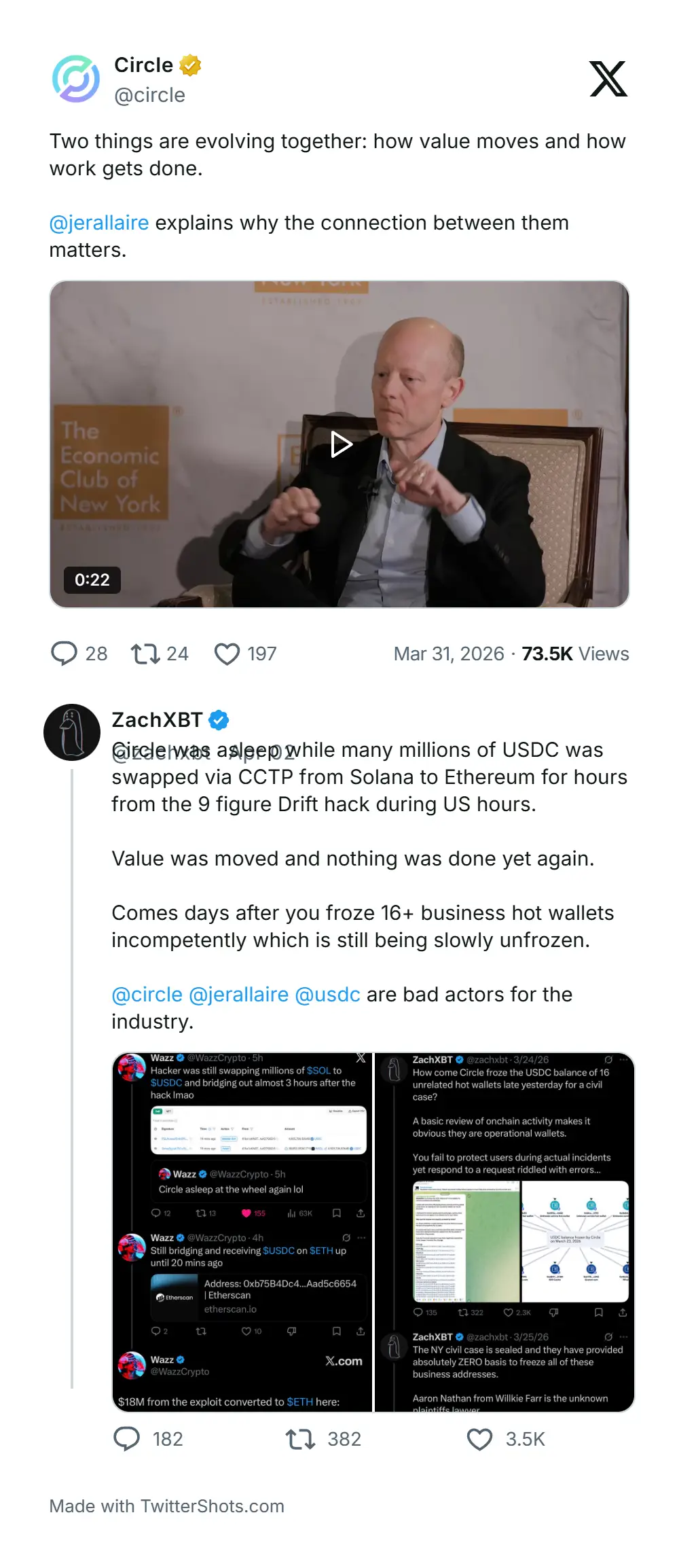
He said $230 million in USDC tied to the exploit was not frozen after being bridged, raising questions about response timing and obligations.
A separate comment by user Molu said, “Circle could freeze it. But they’re not required to,” adding that future regulation such as the GENIUS Act could change expectations around intervention.
Elliptic links attack pattern to North Korea tactics
Blockchain analytics firm Elliptic said the exploit was a likely North Korea-linked operation, citing patterns consistent with prior state-linked attacks.
Elliptic described the operation as “premeditated and carefully staged,” noting the use of test transactions, pre-positioned wallets, rapid consolidation, and cross-chain laundering designed to obscure the origin of funds while maintaining control.
Solana Foundation says incident is not systemic
Solana Foundation CPO Vibhu said the attack was “a very sophisticated attack, the source of which is still being investigated,” and emphasized that “there was no program or smart contract exploit.”
He added, “this ultimately appears to be opsec/social engineering vs contract risk,” and said the breach “could have happened to any protocol protected by a multisig on any chain.”
Vibhu said, “this is an isolated incident and says nothing about Solana DeFi or any other Solana product,” while acknowledging the human impact: “Today was very hard on many people… because nobody deserves this.”
He added that the community would recover, saying the Solana ecosystem would “pick up the pieces and rebuild fast as only Solana can.” That statement sat alongside another security-focused reaction in the provided context: Ledger CTO Charles Guillemet was described as calling the Drift incident a wake-up call for the broader crypto industry and urging stronger security practices.
Drift Opens On-Chain Dialogue With Hackers
Drift escalated its response by initiating direct on-chain communication with wallets holding the stolen funds, signaling a willingness to negotiate with the attackers. The team sent messages to four Ethereum addresses tied to the exploit, stating, “We are ready to speak,” while noting that “critical information” about those involved had already been identified and would be disclosed after third-party verification.
The outreach reflects a common recovery strategy in large DeFi exploits, where projects attempt dialogue to incentivize fund returns. However, expectations remain low if the attackers are indeed linked to North Korea. Curve Finance founder Michael Egorov said the likelihood of recovery would be “zero” in such cases, citing a history of non-cooperation by state-backed groups.
FAQ
What did Drift say happened?
Drift said it was experiencing an active attack on April 1, 2026, froze deposits and withdrawals, and worked with security firms, bridges and exchanges while the incident was investigated.
How large was the reported exploit?
Estimates in the provided context moved from more than $200 million to around $270 million and later roughly $280 million-$285 million as investigators tracked wallet and cross-chain movements more completely.
Did the reporting say this was a smart contract bug?
No confirmed smart contract bug was identified in the provided context. Drift had not yet published a final root cause in the material, while Solana Foundation chief product officer Vibhur Sundaram and several outside experts said the incident appeared tied to operational security, signer approvals and admin access.
What role did durable nonces allegedly play?
Reports said the attacker may have used durable nonces, a Solana transaction feature that keeps pre-signed transactions valid longer, to delay execution of administrative approvals until the moment of the exploit.
Who linked the exploit to North Korea?
Elliptic said the exploit showed hallmarks of a likely North Korea-linked operation. That was presented as a forensic assessment by a blockchain analytics firm, not a confirmed government attribution.
Why was Circle mentioned in the reporting?
ZachXBT said more than $230 million in USDC moved through Circle’s CCTP and argued Circle had several hours to freeze the stolen funds. The source context presented that as a dispute over response and capability, not as a confirmed failure of legal duty.
This article has been refined and enhanced by ChatGPT.