KelpDAO $294M Bridge Exploit Leaves Aave With Bad Debt, DeFi TVL at One-Year Low

Lazarus Group named as likely attacker; Arbitrum froze $71M in stolen ETH before it could escape
TL;DR
- KelpDAO was exploited on April 18, 2026, through a LayerZero bridge attack that allowed $294 million in unbacked rsETH to be minted and used as Aave collateral, creating what is now the largest single DeFi hack of 2026.
- Arbitrum's Security Council froze 30,766 ETH worth approximately $71 million in an emergency vote, while DeFi's total value locked collapsed to a one-year low, losing $13 billion within 48 hours of the attack.
- LayerZero attributed the attack to North Korea's Lazarus Group — specifically the TraderTraitor subgroup — which has now stolen more than $500 million from crypto DeFi platforms in April 2026 alone.
We’ve launched the all-new COIN360 Perp DEX, built for traders who move fast!
Trade 130+ assets with up to 100× leverage, enjoy instant order placement and low-slippage swaps, and earn USDC passive yield while climbing the leaderboard. Your trades deserve more than speed — they deserve mastery.
KelpDAO, an Ethereum-based liquid restaking protocol with $1.57 billion in total value locked, was exploited on April 19, 2026, through its LayerZero-powered cross-chain bridge, allowing an attacker to mint 116,500 unbacked rsETH tokens worth approximately $294 million and immediately deposit them into Aave V3 as collateral to borrow 106,467 ETH (WETH). Lookonchain reported the token movements and Arkham confirmed the transaction trail and fund movements. Because the rsETH used as collateral was unbacked and fraudulently minted, the related Aave positions became effectively unliquidatable, leaving the lending protocol exposed to more than $236 million in bad debt.
The attack exploited a single-point-of-failure in KelpDAO's bridge verification architecture. The protocol used a 1-of-1 DVN (Decentralized Verifier Network) setup to authenticate cross-chain messages on LayerZero. The hackers compromised two RPC nodes feeding data to that DVN verifier, launched a DDoS attack against a third backup RPC node to force a failover, then injected a fraudulent message authorizing the rsETH mint against zero underlying collateral. Security firm Halborn had previously flagged the 1-of-1 DVN configuration in prior warnings, noting it creates a documented single point of failure. Allium, analyzing the verification gap after the incident, stated: "The tools worked as designed. The way they were configured did not."
KelpDAO paused the protocol within 46 minutes of the attack beginning, but the funds had already been moved. The protocol's cross-chain footprint — rsETH existing across more than 20 blockchains — widened the potential blast radius. Meir Dolev, CTO and co-founder of Cyvers, said on April 19, 2026, that KelpDAO was three minutes away from losing an additional $100 million before a blacklist intervention stopped a second attempt. KelpDAO separately reported that the exploiter attempted to drain an additional 40,000 rsETH worth $95 million using further fraudulent tricks but was stopped because the system had already been secured in time. After the attack, malware self-deleted from the compromised RPC nodes, deliberately erasing forensic logs.
LayerZero's Statement and North Korea Attribution
LayerZero said on April 20, 2026, that its DVN was hit by a "highly sophisticated attack" that was "specifically engineered to manipulate or poison downstream RPC infrastructure by compromising a quorum of the RPCs the LayerZero Labs DVN relied upon to verify transactions," adding: "It was not done through an exploit to the protocol, DVN, key management, or other means." LayerZero has since deprecated the affected nodes and fully restored DVN operations, but the financial damage had already been finalized.
LayerZero Labs attributed the attack to North Korea's Lazarus Group, writing: "On April 18, 2026, LayerZero Labs' DVN became the target of a highly sophisticated attack, likely attributable to the Lazarus Group, more specifically TraderTraitor." U.S. authorities had previously connected the Lazarus Group and TraderTraitor apparatus to the $1.5 billion Bybit hack in February 2025. Peter Chung, head of research at Presto Research, said early analysis indicated the issue may have originated in the verification layer rather than in smart contracts themselves.
KelpDAO Blames LayerZero Infrastructure
KelpDAO publicly assigned responsibility to LayerZero on April 21, 2026, stating: "This was an attack on LayerZero's infrastructure. Kelp's own systems were not involved in building or operating that infrastructure." The protocol said it did not choose a risky setup on its own but relied on what LayerZero had recommended since 2024, including the 1-of-1 DVN configuration.
KelpDAO explicitly noted that a 1-of-1 setup is less secure because it creates a single point of failure, and if compromised, malicious actors get a way through. KelpDAO said it was working with LayerZero, auditors, and security experts to investigate the root cause and was concurrently assessing protocol unpausing, impact assessment, and the way forward in coordination with Aave and other key stakeholders. As emergency steps, KelpDAO froze all associated contracts on Layer 2 and the Ethereum mainnet, blocked all wallets associated with the attacker, and implemented SEAL 911.
Aave Freezes Markets, Bad Debt Scenarios Take Shape
Aave founder Stani Kulechov wrote on April 19, 2026: "rsETH has been frozen on Aave V3 and V4, the asset does not have any borrowing power as a measure due to KelpDAO bridge exploit that happened outside of Aave. Both Aave V3 and V4 does not have further exposure to rsETH." Aave also froze WETH reserves across Arbitrum, Base, Mantle, and Linea as a precautionary measure.
KelpDAO noted in a subsequent statement: "Aave's smart contracts were not compromised at any point during this event. All protocol logic, including supply, repayment, and liquidation mechanisms, continued to function as designed." Despite that, the exploit resulted in Aave facing a bad debt estimated between $177 million and $290 million, with total rsETH collateral exposure on Aave reaching approximately $359 million.
@0xngmi, the anonymous founder of DefiLlama, published an analysis laying out two recovery paths for Arbitrum's handling of the frozen ETH and their downstream effect on Aave's bad debt position. In the first scenario, where every rsETH holder is treated equally regardless of whether they hold on L1 or L2, all holders would automatically be down approximately 18.5% on their holdings — the share of rsETH supply stolen before the Arbitrum ETH recovery — with Aave on the hook for approximately $216 million, requiring it to deplete its treasury and Umbrella fund and potentially liquidate tokens.
In the second scenario, where losses are localized to rsETH holders on L2s since that is where the exploit occurred, Aave bad debt on Arbitrum would fall from approximately $88 million to $17 million, an 80% reduction, but total Aave bad debt under that path would reach approximately $341 million on its $359 million exposure.
The fallout from the KelpDAO exploit quickly extended beyond direct losses, exposing deeper liquidity stress and structural fragility across DeFi lending markets. Aave saw significant capital flight in the days following the attack, with billions in deposits exiting as users reacted to rising uncertainty around protocol exposure and collateral integrity.
At the same time, liquidity conditions on Aave deteriorated sharply. Circle proposed emergency changes to the USDC interest rate model after the pool became effectively locked, operating at 99.87% utilization with almost no available liquidity. The proposal argued that the existing rate curve failed to restore balance, suggesting sharply higher yields of up to 40–50% to attract fresh capital and normalize market function.
Elsewhere, protocols moved to limit further damage. Privacy-focused payment protocol Umbra shut down its front-end interface after detecting that stolen funds were being routed through its system, although direct smart contract access remained possible.
Arbitrum Emergency Vote Freezes $71M
Arbitrum's Security Council intervened in an emergency vote requiring nine out of twelve council members to agree, described as taking hours of technical, ethical, and political deliberation, to freeze 30,766 ETH valued at approximately $71 million at the time — catching the funds before they could be fully bridged out to Ethereum mainnet.
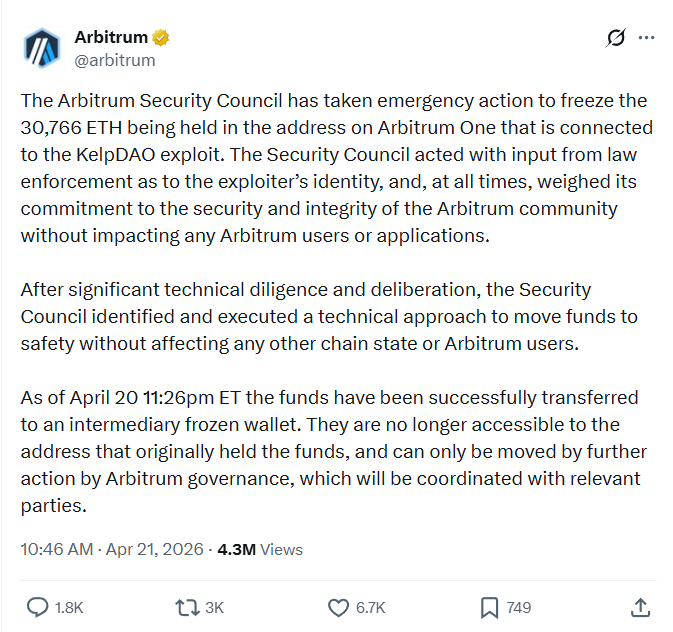
The frozen amount represents approximately one quarter of the $292 million total stolen, with more than $200 million still moving across the ecosystem. The intervention immediately sparked debate over whether centralized emergency action conflicts with core decentralization principles. Any further action on the frozen ETH is required to go through governance, meaning the community or its representatives will decide the funds' fate — a process that sets a significant precedent for future Layer 2 governance responses to exploits.
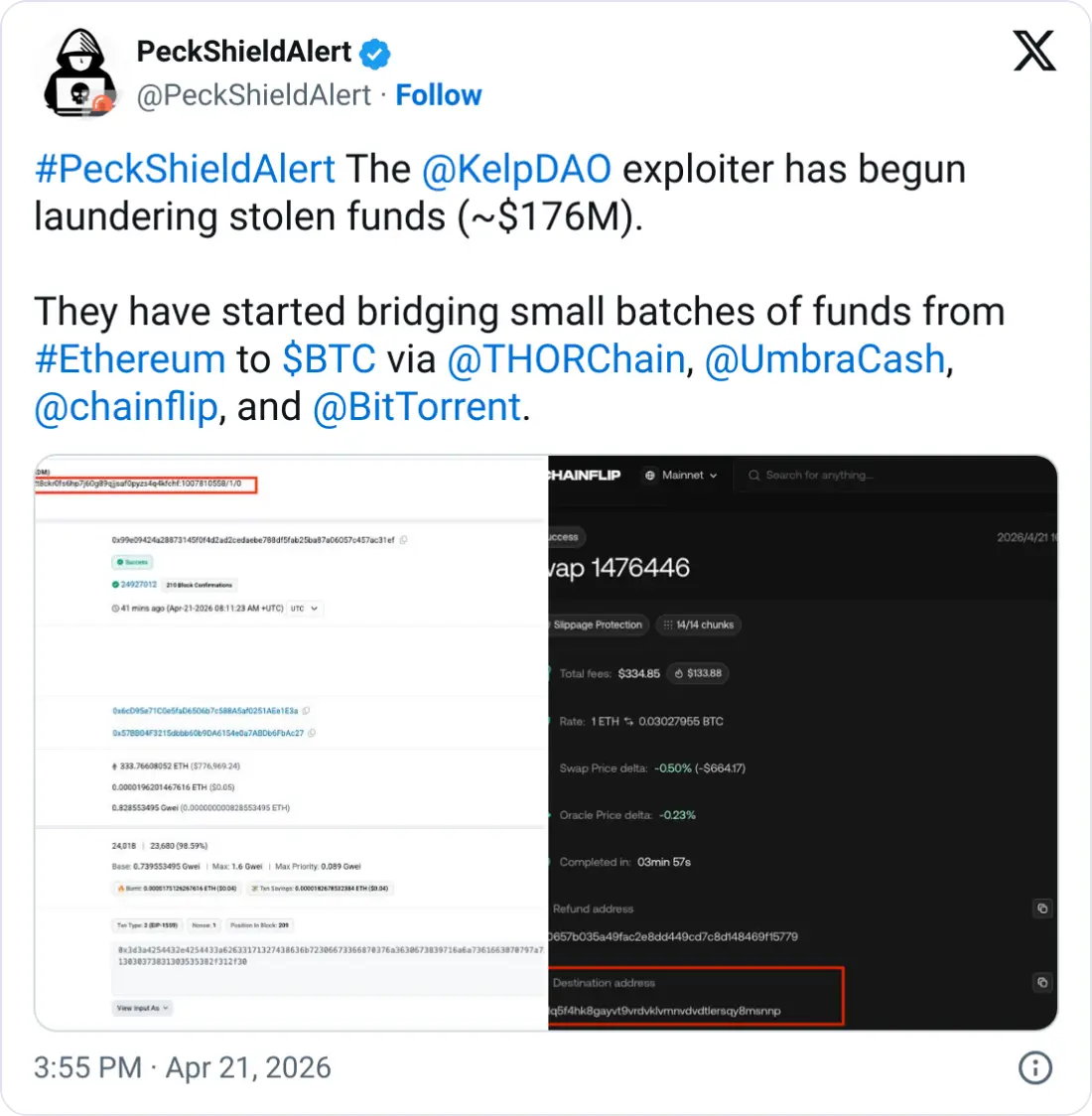
Shortly after Arbitrum froze the assets, the hacker began laundering assets by transferring funds across multiple blockchain networks. On-chain analysts reported that around $1.5 million in stolen ETH was moved from Ethereum to Bitcoin via THORChain, while an additional $78,000 was routed through the privacy protocol Umbra. Security firm PeckShield estimates that roughly $176 million is being transferred through various protocols, intensifying concerns about recovery.
@0xngmi also noted on April 21, 2026: "If they return to Kelp and Kelp adds it to the pool to cover losses the bad debt on Arbitrum will be higher as well, as this recovered money will need to be split among all L2s." He stated the $71 million recovery "gives Aave a lot of breathing room on the very difficult decisions that it faces."
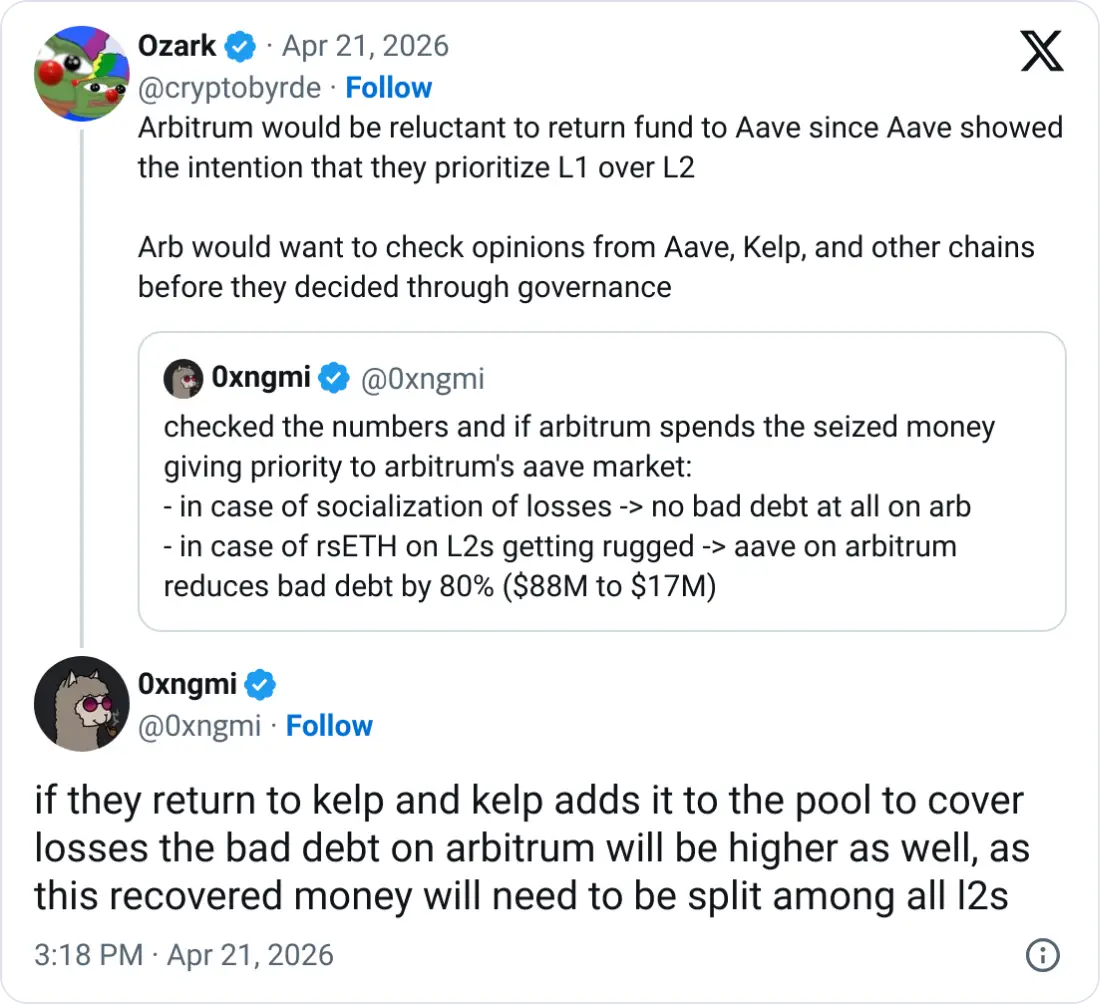
He added that Aave's Umbrella fund does not cover all L2s, so Aave would have discretion to choose which markets to save and which to allow to fail — a path he noted could lead to dissatisfaction and potential litigation.
Protocol Responses Across the Ecosystem
Multiple protocols took immediate defensive action in the days following the exploit. Axelar Network said on April 19, 2026, that the breach was likely enabled by a single-validator configuration rather than a multi-validator setup. Katana paused its OFT path on Vaultbridge, which relied on a 2/3 DVN configuration. Bridging through Agglayer remained operational because it uses zero-knowledge proof verification rather than proof-of-authority multisigs. Ethena said it had "no exposure to the rsETH exploit" but paused its LayerZero OFT bridges from Ethereum mainnet "out of an abundance of caution."
Lido Finance also paused related bridge activity. BitGo said: "User funds remain secure and updates will be shared as more information becomes available," after BitGo and BiT Global Trust took down the LayerZero OFT DVNs for Wrapped Bitcoin. Polygon said on April 19, 2026, that its chain, Agglayer, and broader ecosystem were unaffected and had safely processed over $2 trillion in transactions to date.
Tron founder Justin Sun publicly urged the attacker to negotiate on April 19, 2026, writing: "OK — Kelpdao hacker, how much you want? Let's just talk. With KelpDAO's help, of course. It's simply not worth it to sacrifice both Aave and KelpDAO and let them go down over this hack." Arkham data showed Sun subsequently withdrew 65,584 ETH worth about $154 million from Aave and deposited it into Spark; his remaining Aave exposure fell to $380 million while his Sky and Spark holdings rose to $2.13 billion.
OneKey founder Yishi described the layered failure: "KelpDAO dismantled the lock on its own door, LayerZero is selling the kind of door where you can pick the lock yourself, and Aave assumed the neighbor's door was definitely locked tight." Yishi stated: "The best outcome is to negotiate with the hacker, offer a 10–15% bounty, get the bulk of it back," adding that if talks fail, LayerZero should step in financially because it has "the deepest pockets and the most long-term skin in the game."
He also said: "KelpDAO is the broke one here — either make it up with tokens + future revenue, or just package the whole project and sell it off to L0 or BMNR," and warned: "WETH depositors absolutely cannot take a haircut," because losses there could spread through Morpho, Spark, Fluid, and Euler. He added: "I believe Aave can weather this."
TVL and Token Price Impact
The attack triggered the sharpest DeFi capital exodus in over a year. Aave's TVL fell approximately 18% to $17.8 billion within 24 hours and nearly 30% over seven days, dropping from $26.39 billion on April 18 to approximately $17.51 billion in under 48 hours. DeFi-wide TVL fell from $99.497 billion to $86.286 billion in less than two days, per DefiLlama data, reaching its lowest point in twelve months. Ethereum alone lost $10.34 billion in TVL, falling to approximately $46.16 billion. All top 20 DeFi chains posted net outflows, and total outflows topped $10 billion in the 24 hours following the attack.
The following table summarizes the key TVL figures before and after the exploit, with data from DefiLlama:
Lookonchain said whales began selling AAVE after the exploit became public. Binance inflows rose above 236,000 AAVE, compared with a normal 31,000 average, and total exchange inflows crossed 355,000 AAVE worth approximately $32 million. CryptoQuant data showed exchange reserves climbed past 180,000 tokens. AAVE fell more than 20% in the first 24 hours and traded at approximately $92.06 in the immediate aftermath.
According to COIN360 crypto price data, AAVE was subsequently down approximately 2.5% over 24 hours, with UNI and LINK each down less than 1%. COIN360 market data also showed AAVE recovering to approximately $93.59, up from its $80 bottom on April 20, as sentiment stabilized following the Arbitrum freeze news. Santiment reported that Aave sentiment stopped dropping to new lows after news of the Arbitrum Security Council's ETH confiscation hit the headlines.
LayerZero's ZRO token fell more than 22% over 24 hours to approximately $1.52, down from above $2 two days earlier, before recovering to approximately $1.63, up 5.57%, as of April 21. Onchain Lens data shared on X said a whale holding a ZRO long position on Hyperliquid lost $2.88 million in liquidation and was still sitting on another $750,000 in unrealized losses, for a total position loss of approximately 428.98 million units.
Peter Chung said the episode showed how interconnected DeFi protocols can transmit shocks beyond the initial point of failure. Ted Pillows wrote: "Every protocol is taking a hit now. Not a great 24 hours for crypto's image."
Rate-Limit Proposals and April 2026 Hack Totals
The exploit renewed calls for built-in rate limits across bridges and lending systems. Ethena contributor Guy Young wrote: "We built a solution on top of the standard OFT to throttle cross chain transfers at $10m per hour for every DVN, in addition to the $10m per block rate limit on the mint contract. The former would have prevented Kelp, the latter Resolv." That setup caps potential damage at $10 million per chain per hour even if a DVN is fully compromised.
Keone Hon, CEO and co-founder of Monad, argued on April 19, 2026, that pooled lending protocols should use "smart caps" on how fast collateral supply can grow, writing: "Feels like pooled lending protocols would benefit from a rate limit on the supply of an asset being deposited for collateral. Like, if the current supply is 100m and the supply cap is 300m, the supply should only be allowed to go to 110m in the next 10 minutes. Nobody needs to…" Hon said that kind of control would have saved rsETH depositors $200 million in this case and pointed to the Resolv hack in March, where an attacker could mint infinite tokens but extracted only $24 million because exit pathways were constrained.
According to data from DefiLlama, by April 20, 2026, cumulative crypto hack losses for the month had reached $606,215,950 across 12 incidents, making April the worst month for crypto exploits since February 2025, when the $1.4 billion Bybit breach pushed that month's total to $1.466 billion. April's total was nearly four times larger than the combined first-quarter 2026 figure of $165.5 million.
KelpDAO at $292–$294 million and Drift Protocol at $285–$286 million accounted for approximately 95% of April's losses and roughly 75% of the 2026 year-to-date total of $771.8 million across 47 incidents. Monthly hack losses were up 1,368% from March, while incident frequency rose 68% year over year.
Industry Backs Recovery While Calling for Standards
Haseeb Qureshi, managing partner at Dragonfly, said on April 20, 2026: "AAVE might take on some bad debt, but it has the equity to pay it," backing DeFi to learn from its failures and adding that Aave and affected protocols were in "completely recoverable" positions. Qureshi said: "DeFi learns through failures. The important thing is that these failures are not fatal. The heart of DeFi is risk-averse and robust." @0xngmi added: "DeFi is gonna take a hit, but it will not die." Drift Protocol had separately struck a deal with Tether and other parties to relaunch its platform with approximately $150 million in backing.
Michael Egorov, founder of Curve Finance and Yield Basis, used the incident to call for formal industry-wide safety standards, saying on April 21, 2026: "All issues like this should be prevented before they happen. We should probably come together and develop safety standards for DeFi." He argued that critical dependencies should be distributed wherever possible and that, where centralization cannot be eliminated, trust should be split across multiple parties. Egorov called for coordinated action led by major ecosystem players, including the Ethereum and Solana Foundations, to establish shared guidelines for building and verifying secure protocols.
North Korea's Broader 2026 Campaign
In just under three weeks of April 2026, cyber operatives linked to the Democratic People's Republic of Korea stole more than $500 million from crypto DeFi platforms, pushing North Korea's illicit crypto haul for the year well past the $700 million mark.
The twin exploits — Drift Protocol on April 1, 2026, drained of approximately $286 million, and KelpDAO on April 18, 2026 — account for the bulk of that figure. Blockchain intelligence firm Elliptic connected the on-chain laundering methodologies, transaction sequencing, and network-level signatures in the Drift hack to previously established DPRK attack vectors, noting it was the 18th such incident Elliptic had tracked in 2026 alone.
Cyvers said that North Korea-linked attackers are "showing increased sophistication and investing more resources, both in preparation and execution," and consistently find the weakest link, adding: "In this case, it was a third party rather than the protocol's core infrastructure."
A six-month investigation by the Ketman Project, operating under the Ethereum Foundation's ETH Rangers security program, found that approximately 100 North Korean cyber operatives are currently embedded inside various blockchain companies, operating under fabricated identities, passing standard HR screenings, gaining access to internal code repositories, and sitting within product teams for months or years before initiating a calculated attack.
ZachXBT independently exposed a specialized DPRK network generating approximately $1 million a month using fraudulent personas to secure remote work; that scheme has processed over $3.5 million since late 2025. According to Chainalysis, DPRK-linked hackers stole a record $2 billion in 2025, accounting for approximately 60% of all global cryptocurrency thefts that year. Factoring in 2026 activity, North Korea's all-time crypto asset haul is estimated at $6.75 billion.
Lazarus Group operatives rely heavily on Chinese-language guarantee services, deep OTC broker networks, and complex cross-chain mixing services for laundering — a pattern that points to structural constraints and geographically limited fiat off-ramps. Terence Kwok, founder of Humanity, said: "What's striking is how often the damage still comes down to the same weak points around access control and single points of failure. That tells you the industry still has some basic security discipline issues it has not solved."
FAQ
What was actually exploited in the KelpDAO attack?
KelpDAO's LayerZero-powered cross-chain bridge, specifically its single 1-of-1 DVN verifier node configuration.
Why couldn't Aave simply liquidate the bad rsETH collateral positions?
The rsETH used as collateral was unbacked, making those Aave positions effectively unliquidatable with no recoverable value.
How much of the stolen funds have been recovered so far?
Arbitrum froze approximately $71 million (30,766 ETH), roughly one quarter of the $292 million total stolen.
Who is attributed as the likely attacker behind the KelpDAO exploit?
LayerZero named North Korea's Lazarus Group, specifically the TraderTraitor subgroup, as the likely threat actor.
This article has been refined and enhanced by ChatGPT.