Wasabi Protocol Drained After Admin Key Compromise
Exploit Hit Multichain Vaults During April Hack Surge
TL;DR
- Wasabi Protocol lost about $5.5 million after a compromised private key allowed an attacker to change admin rights and drain vaults across multiple networks.
- Blockaid traced the root cause to wasabideployer.eth, the only address holding ADMIN_ROLE in Wasabi’s PerpManager AccessManager.
- April crypto hack losses reached $629.7 million across more than 25 hacks, the worst monthly total since February 2025.
We’ve launched the all-new COIN360 Perp DEX, built for traders who move fast!
Trade 130+ assets with up to 100× leverage, enjoy instant order placement and low-slippage swaps, and earn USDC passive yield while climbing the leaderboard. Your trades deserve more than speed — they deserve mastery.
Wasabi Protocol was drained for about $5.5 million after an attacker gained access to a compromised private key, changed admin rights and emptied vaults across Ethereum, Base, Blast and Berachain, with the latest estimate superseding earlier counts of roughly $4.55 million or “over $5 million.”
Wasabi Protocol told users, “We’re aware of an issue and are actively investigating. As a precaution, please do not interact with Wasabi contracts until further notice,” while the project had not fully explained the nature of the attack in the initial moments after losses were discovered. The breach affected a DeFi platform used for trading and lending, including a venue for long-tail assets, NFT tokens and meme tokens.
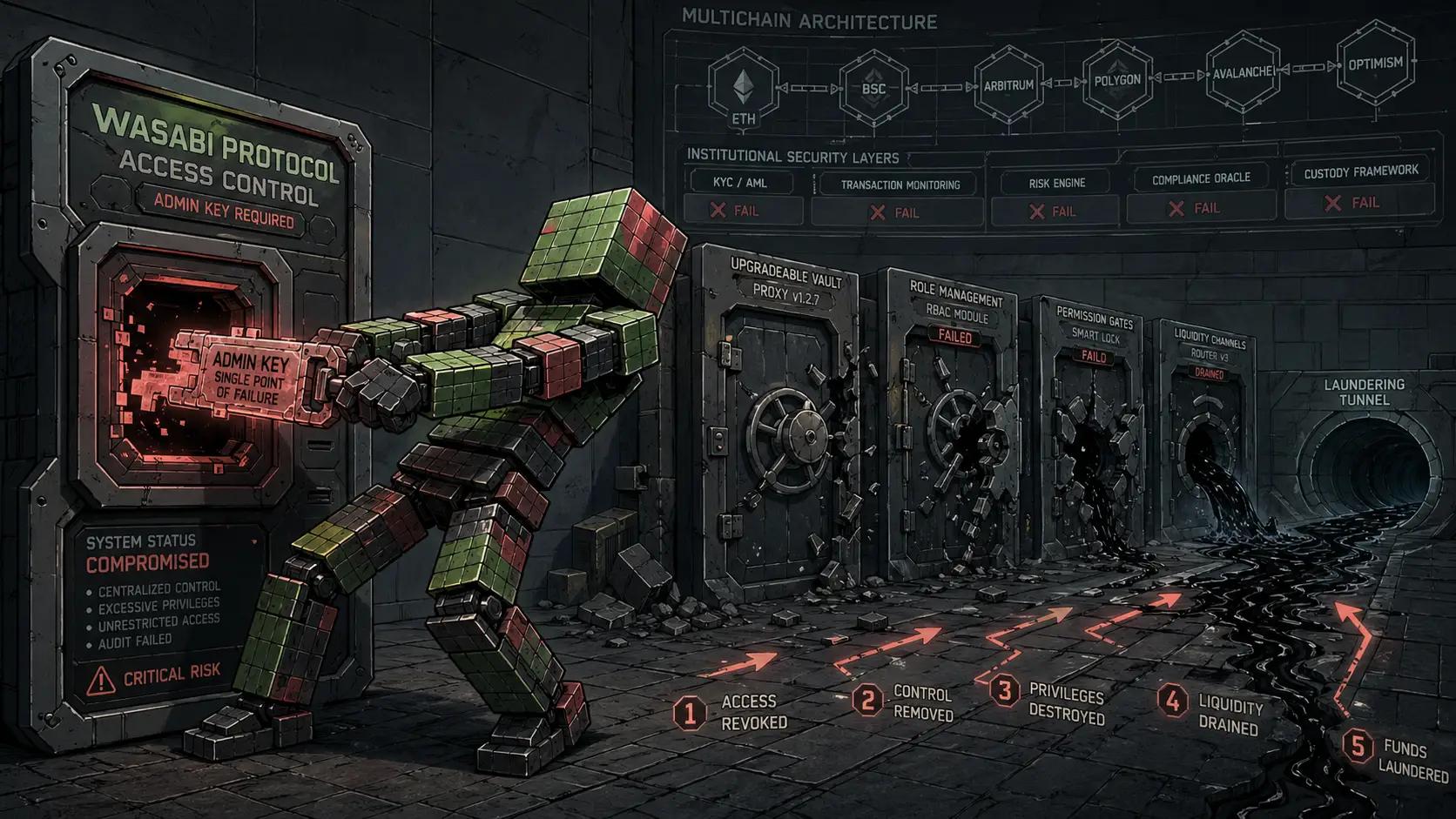
Blockaid traced the root cause to wasabideployer.eth, the only address holding ADMIN_ROLE in Wasabi’s PerpManager AccessManager. The attacker used that control path to call grantRole on the deployer EOA with zero delay, immediately turning the orchestrator contract into an admin. The exploit was described as a compromised admin-key failure rather than a conventional smart contract logic bug.
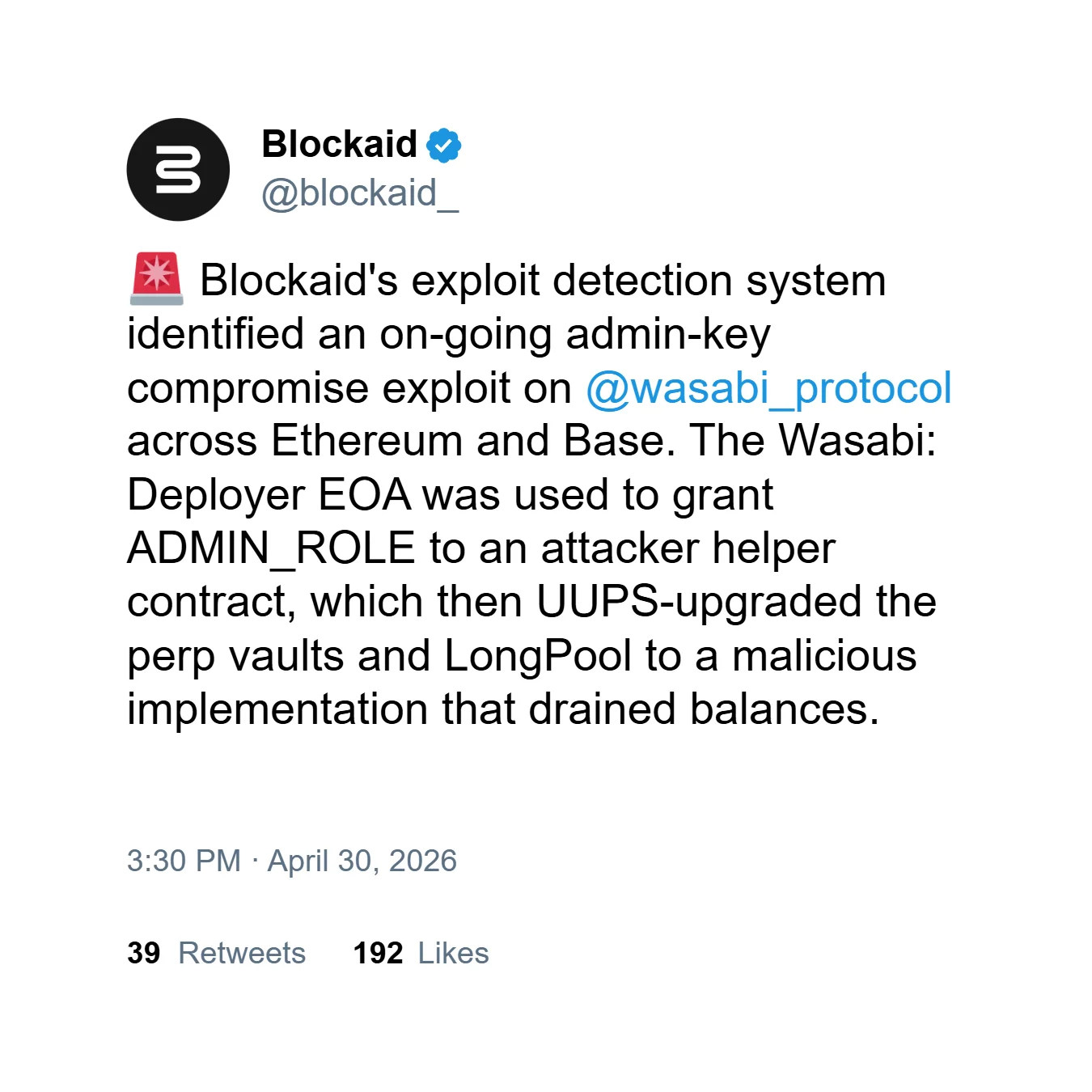
The attacker then used the compromised admin path to UUPS-upgrade perpetual vaults and the LongPool to a malicious implementation. That allowed user balances to be siphoned from Wasabi’s perpetuals vaults and LongPool. On-chain researcher ZachXBT said Wasabi Protocol was not sufficiently decentralized because a single wallet controlled multiple critical functions, while researchers identified the likely cause as a leaked private key controlling upgradeable, permissionless vaults with no multisig approval, timelock or voting process.
Tokens and Networks Affected
The stolen assets covered multiple chains and token types, with $1.9 million of the losses held in WETH. The funds were bridged to Ethereum, consolidated and partially sent through Tornado Cash, turning the incident into a laundering case after assets were moved away from the original vaults.
Wasabi and Spicy LP-share tokens from affected vaults were flagged as compromised, with redemption value approaching zero. Tokens minted from compromised vaults were described as practically worthless, even though user wallets may still show book value that cannot be redeemed. Users with active approvals to receive tokens were told to revoke them, while other users were advised to flag affected tokens as compromised wherever possible.
Virtuals Protocol, which often launches new AI agent tokens through Wasabi, said it suffered no losses and preemptively stopped all interactions with vault smart contracts. Wasabi Protocol had $8.52 million in total value locked just before the hack, and its native DEX had started recording higher trading volumes in March based on DeFi Llama data, though the exploit was not directly linked to that activity.
Blockaid said the same attacker, orchestrator and strategy bytecode tied the Wasabi incident to earlier activity targeting the protocol. That finding made the exploit appear less like a one-off accident and more like repeat operational targeting of the same weak control structure.
April Hack Losses Reached Their Highest Level Since February 2025
The Wasabi breach occurred during a wider April acceleration in crypto exploits, when total crypto hack losses reached $629.7 million across more than 25 hacks. April became the worst month for crypto hacks since February 2025, when losses hit $1.47 billion.
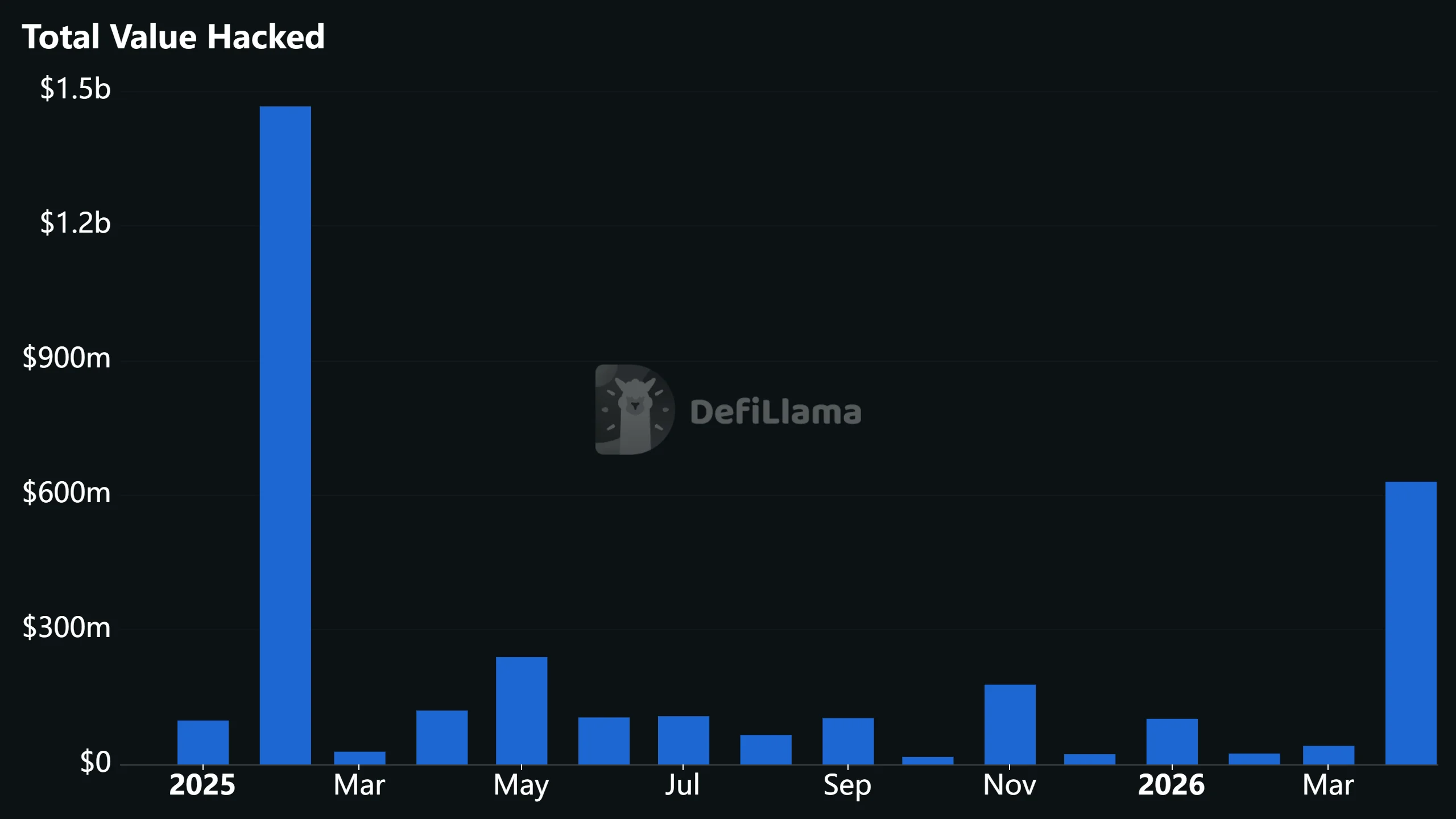
DeFi dominated April’s losses, with KelpDAO and Drift Protocol together accounting for most of the monthly total. The month’s major incidents showed that the largest risks were increasingly tied to bridges, privileged access and operational failures, rather than simple smart contract bugs alone.
A separate update around the same exploit wave said Sweat Economy’s drain was later described as a foundation rescue, not a hack, leaving the final confirmed state as a loss event whose characterization shifted away from a straightforward external hack. Aftermath Finance and Syndicate Commons bridge added smaller but still relevant incidents to the same late-April cluster.
Yaniv Nissenboim, head of security solutions at Chainalysis, said April’s spike reflected more sophisticated, multi-stage attacks targeting offchain infrastructure rather than smart contract vulnerabilities. “What connects these incidents is that well-resourced attackers are finding novel ways to exploit the seams between on-chain protocols and the offchain systems they depend on,” Nissenboim said.
Nissenboim said attack entry points included compromised RPC nodes, breaches of cloud key management systems and long-running social engineering campaigns. He said on-chain transactions can still appear legitimate after infrastructure or human-access layers have already been compromised, and said real-time monitoring and automated safeguards are becoming critical because abnormal minting patterns and cross-chain inconsistencies can be detected instantly.
Nissenboim also said rapid detection helped prevent a second theft of roughly $95 million during the KelpDAO incident. Cyvers co-founder Meir Dolev said April’s spike was driven by a small number of “precision strikes,” with attackers increasingly targeting high-liquidity protocols. Dolev said the month ranked among the worst for DeFi hacks in five years because losses were driven by social engineering and cross-chain complexity.
Hacken said April marked the worst month on record for DeFi losses, driven largely by breaches involving Kelp and Drift, and attributed the attacks to actors linked to the Democratic People’s Republic of Korea (DPRK). Standard Chartered’s analysts led by Geoffrey Kendrick framed the KelpDAO incident as a sign of DeFi’s growing resilience rather than a fatal sector failure.
“While the recent KelpDAO theft and its impact on AAVE have raised questions around continued DeFi banking growth, we expect growth to remain on track as a maturing DeFi industry puts solutions in place to reduce vulnerabilities,” Kendrick said.
AI-Hacker Theory Remains Separate From the Confirmed Wasabi Failure
The Wasabi incident revived speculation that AI tools may be accelerating DeFi exploit discovery, but the confirmed mechanics of the Wasabi breach pointed to compromised admin access, single-EOA control and upgradeable vault infrastructure. DeFi analyst @DefiIgnas said recent hacks shared a pattern of targeting older or more obscure protocols and that targets were probably selected using AI, with any vault over $100,000 becoming a target.
Developer Vitto Rivabella floated the strongest AI-hacker theory, writing, “Wild conspiracy theory about the recent DeFi hacks: North Korea has trained its own, state funded, version of Mythos using the insane amounts of data obtained by hacking DeFi protocols over the last 10 years. Now they’re just letting their AI DeFi hacker run free and won’t stop cashing in until someone stops them.”
Rivabella also pointed to the speed of recent incidents, asking, “It’s not about the type, it’s about the quantity – what is it now, 7 hacks in the last 5 days?” James Seyffart separately amplified the broader concern by asking, “People are asking — Is AI the end of crypto?”
FAQ
What caused the Wasabi Protocol exploit?
A compromised admin key allowed the attacker to change roles and upgrade vaults maliciously.
How much did Wasabi Protocol lose?
The latest and most explicit estimate put losses at about $5.5 million.
Which networks were affected?
Ethereum, Base, Blast and Berachain vaults were affected.
Was the Wasabi exploit confirmed as an AI attack?
No. The confirmed issue was compromised privileged access; the AI angle remains speculation.
This article has been refined and enhanced by ChatGPT.